API, SDK, Technology |
Understanding the Difference: API vs SDK
When it comes to software development, two terms that often come up in discussions are API and SDK. Both are essential tools for developers, but they serve different purposes and have distinct functionalities. In this article, we will delve into the details of API and SDK, their differences, and how they are used in the world of software development.
API: Application Programming Interface
API, which stands for Application Programming Interface, is a set of protocols, tools, and definitions that allow different software applications to communicate with each other. It defines the methods and data formats that applications can use to request and exchange information. In simpler terms, an API acts as a bridge between different software systems, enabling them to interact and share data seamlessly.
APIs are commonly used to enable integration between different software applications or services. For example, social media platforms provide APIs that allow developers to integrate features such as sharing posts or retrieving user data into their own applications. Similarly, payment gateways offer APIs to facilitate secure transactions within third-party applications.
One of the key characteristics of APIs is that they are typically language-agnostic, meaning they can be used with different programming languages. This flexibility makes APIs widely accessible and versatile for developers across various platforms and technologies.
SDK: Software Development Kit
On the other hand, a Software Development Kit, or SDK, is a comprehensive set of tools, libraries, and documentation that provides developers with the resources they need to build software applications for a specific platform, framework, or programming language. An SDK typically includes a range of components such as APIs, sample code, debugging tools, and tutorials to streamline the development process.
SDKs are designed to offer a more complete and integrated development experience by providing developers with everything they need to create applications for a particular platform. For example, a mobile SDK may include APIs for accessing device features such as the camera or GPS, along with sample code and development tools tailored for building mobile apps.
Unlike APIs, SDKs are often platform-specific and may be optimized for a particular programming language or framework. This specialization allows SDKs to offer deeper integration with the platform and access to specific features that are not available through generic APIs.
Key Differences and Use Cases
Now that we have a clear understanding of API and SDK, let’s highlight the key differences and explore their respective use cases.
1. Purpose and Functionality
– API: APIs primarily focus on defining the methods and protocols for communication between different software systems. They act as intermediaries that enable seamless interaction and data exchange.
– SDK: SDKs are geared towards providing a comprehensive set of tools, resources, and libraries to facilitate the development of applications for a specific platform or framework. They offer a more holistic approach to software development by including various components and documentation.
2. Flexibility and Integration
– API: APIs are designed to be language-agnostic, allowing them to be used with different programming languages and technologies. They offer flexibility in integrating with diverse systems and applications.
– SDK: SDKs are often platform-specific and may be tailored for a particular programming language or framework. They provide deeper integration with the platform and access to specific features and functionalities.
3. Development Experience
– API: Working with APIs involves utilizing predefined methods and data formats to interact with external systems. Developers can leverage APIs to add specific features or functionality to their applications without the need to build them from scratch.
– SDK: SDKs offer a more immersive development experience by providing a complete set of tools, sample code, and resources tailored for a specific platform. They streamline the development process and enable developers to leverage platform-specific features effectively.
Conclusion
In conclusion, both API and SDK are essential components of software development, each serving distinct purposes and offering unique benefits. While APIs facilitate seamless communication and integration between different software systems, SDKs provide a comprehensive set of tools and resources for building applications tailored to specific platforms or frameworks. Understanding the differences between API and SDK is crucial for developers to make informed decisions and effectively leverage these tools in their projects.
Whether you are integrating third-party services using APIs or developing applications for specific platforms with SDKs, having a clear grasp of these concepts will undoubtedly enhance your proficiency as a software developer.
Practical Applications of APIs and SDKs
APIs and SDKs have a wide range of practical applications across various industries and sectors. Let’s explore some common use cases for both:
APIs in Action
1. E-commerce Integration: E-commerce platforms often provide APIs that allow businesses to integrate their online store with other services, such as payment gateways, shipping providers, or inventory management systems. This enables seamless data sharing and streamlined operations.
2. Social Media Integration: Social media platforms, such as Facebook, Twitter, and Instagram, offer APIs that enable developers to build applications that can interact with the platform’s data and features. This allows users to share content, access user profiles, and even automate social media management tasks.
3. Mapping and Location-based Services: Geolocation APIs, like the ones provided by Google Maps or OpenStreetMap, allow developers to integrate maps, directions, and location-based features into their applications. This is particularly useful for navigation apps, ride-sharing services, and location-based marketing campaigns.
4. Financial and Banking APIs: The financial industry is increasingly adopting APIs to facilitate secure and efficient transactions, access customer data, and enable fintech applications. Banks and financial institutions can offer APIs that allow third-party applications to perform tasks like account management, money transfers, and credit checks.
5. Weather and Environmental APIs: APIs from weather services, such as OpenWeatherMap or AccuWeather, provide developers with access to real-time weather data, forecasts, and historical records. This information can be integrated into a wide range of applications, from weather apps to agriculture-related software.
SDKs in Action
1. Mobile App Development: Mobile operating systems, like iOS and Android, provide SDKs that help developers build native mobile applications. These SDKs include APIs, tools, and sample code that enable access to device features, such as the camera, GPS, and sensors, as well as integration with platform-specific services and user interface components.
2. Game Development: Game engines, such as Unity and Unreal Engine, offer comprehensive SDKs that simplify the game development process. These SDKs include tools for 3D modeling, physics simulation, audio integration, and a wide range of other features that are essential for creating high-quality video games.
3. Internet of Things (IoT) Development: IoT platforms and device manufacturers often provide SDKs to help developers build applications for connected devices. These SDKs typically include APIs, libraries, and tools for interacting with IoT sensors, managing device data, and integrating with cloud-based services.
4. Cloud Computing and Web Services: Cloud providers, such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform, offer SDKs that simplify the development and deployment of cloud-based applications. These SDKs provide access to a wide range of cloud services, including storage, databases, and serverless computing, making it easier for developers to leverage the power of the cloud.
5. Desktop and Enterprise Software: Software vendors often provide SDKs to enable integration and customization of their desktop or enterprise-level applications. These SDKs can include APIs, libraries, and tools that allow developers to build add-ons, plugins, or custom integrations that extend the functionality of the core software.
Advantages and Disadvantages of APIs and SDKs
Both APIs and SDKs offer numerous advantages, but they also come with some potential drawbacks. Let’s explore the key pros and cons of each:
Advantages of APIs
1. Flexibility and Interoperability: APIs are designed to be language-agnostic, allowing developers to integrate them into a wide range of applications and platforms, regardless of the underlying technology stack.
2. Scalability and Efficiency: APIs enable efficient data exchange and integration, as they provide a standardized way for different systems to communicate. This can help improve scalability and reduce the complexity of integrating multiple systems.
3. Reduced Development Time: By leveraging existing APIs, developers can save time and resources by not having to build certain functionalities from scratch. This allows them to focus on developing the core features of their application.
4. Monetization Opportunities: Some organizations monetize their APIs by charging for access or usage, creating a new revenue stream for the API provider.
Disadvantages of APIs
1. Dependency on External Systems: By relying on external APIs, developers may introduce a level of dependency on the stability and availability of those systems. If an API experiences downtime or changes, it can impact the functionality of the dependent application.
2. Security and Privacy Concerns: Integrating with external APIs raises potential security and privacy risks, as developers need to ensure the secure handling of sensitive data and comply with any applicable regulations.
3. Versioning and Compatibility Issues: API providers may introduce breaking changes or version updates, which can require developers to update their applications to maintain compatibility and functionality.
Advantages of SDKs
1. Streamlined Development: SDKs provide a comprehensive set of tools, libraries, and documentation that simplify the development process, allowing developers to leverage platform-specific features and functionalities more effectively.
2. Improved Integration and Performance: SDKs are designed to be tightly integrated with the target platform or framework, enabling deeper integration and often resulting in better application performance compared to using generic APIs.
3. Enhanced Developer Productivity: SDKs typically include sample code, tutorials, and debugging tools that help developers get up and running quickly, increasing their productivity and reducing the time-to-market for their applications.
4. Consistent User Experience: By using an SDK, developers can ensure a consistent user experience that aligns with the platform’s design guidelines and conventions, resulting in a more seamless and intuitive application for end-users.
Disadvantages of SDKs
1. Platform-specific Dependency: SDKs are often tailored for specific platforms or frameworks, which can limit the portability and cross-platform compatibility of applications built using them.
2. Maintenance and Upgrades: Developers must keep track of SDK updates and ensure their applications remain compatible as the platform evolves, which can require additional time and resources.
3. Limited Flexibility: While SDKs provide a more comprehensive development experience, they may not offer the same level of flexibility as working directly with APIs, especially when it comes to integrating with external systems or third-party services.
4. Vendor Lock-in: Relying heavily on a specific SDK can lead to a certain level of vendor lock-in, as transitioning to a different platform or technology may require a significant rewrite of the application.
Choosing Between API and SDK: Factors to Consider
When deciding whether to use an API or an SDK for your software development project, there are several key factors to consider:
1. Project Requirements and Scope
Evaluate the specific needs of your project and the level of platform integration required. If you need to integrate with multiple, diverse systems, an API-based approach may be more suitable. On the other hand, if you’re building an application that heavily relies on platform-specific features and functionalities, an SDK might be the better choice.
2. Development Team Expertise
Consider the skill set and experience of your development team. If they are familiar with the target platform or framework, an SDK may be the preferred option, as it can leverage their existing knowledge and streamline the development process. If your team is more comfortable with a wider range of technologies, an API-based integration may be more suitable.
3. Performance and Optimization
Evaluate the performance requirements of your application. If you need to maximize performance and leverage platform-specific optimizations, an SDK-based approach may be more advantageous. However, if performance is not a critical factor, an API-based integration can still be a viable option.
4. Portability and Flexibility
Determine the importance of cross-platform compatibility and flexibility in your project. If you need to support multiple platforms or maintain the ability to easily integrate with other systems in the future, an API-based approach may be the better choice. Conversely, if your application is primarily focused on a single platform, an SDK may be the more suitable option.
5. Maintenance and Upgrades
Consider the long-term maintenance and upgrade requirements of your application. APIs may be more resilient to changes, as they typically have a more consistent and standardized interface. SDKs, however, may require more frequent updates to maintain compatibility as the underlying platform evolves.
Ultimately, the decision to use an API or an SDK will depend on the specific needs and constraints of your project. It’s often helpful to evaluate the tradeoffs and weigh the advantages and disadvantages of each approach to determine the best fit for your software development requirements.
Conclusion
In the world of software development, both APIs and SDKs play crucial roles in enabling integration, streamlining development, and empowering developers to build innovative applications. Understanding the key differences between these two concepts is essential for making informed decisions and selecting the most appropriate solution for your project.
APIs provide a flexible and language-agnostic way to enable communication and data exchange between different software systems, while SDKs offer a more comprehensive and platform-specific development experience. By considering factors such as project requirements, team expertise, performance needs, and long-term maintenance, you can determine the best approach to leverage the power of APIs and SDKs effectively.
As technology continues to evolve and the demand for seamless integration and efficient development grows, the understanding and strategic use of APIs and SDKs will become increasingly crucial for software developers and organizations to stay competitive and deliver exceptional applications that meet the needs of their users.

Algorithm, programing, Technology |
When creating an OTP generator program, it is essential to understand the underlying principles and algorithms behind it. The first step is to decide on the type of OTP generator to implement. There are several options available, including time-based OTPs (TOTPs) and event-based OTPs (HOTPs).
If you choose to implement a TOTP, you will need to use a cryptographic hash function, such as SHA-1 or SHA-256, to generate the OTP. TOTPs are time-based, meaning that the generated OTP changes periodically, typically every 30 seconds. To achieve this, you will need to incorporate the current time into the OTP generation process. This can be done by converting the current time into a timestamp and dividing it by a predefined time step, such as 30 seconds.
On the other hand, if you decide to implement an HOTP, you will need to use a counter-based approach. HOTPs generate a unique OTP for each login attempt, incrementing a counter value each time. The OTP is derived from the counter value using a cryptographic hash function. This ensures that each OTP is unique and cannot be predicted without knowledge of the counter value.
Regardless of the type of OTP generator you choose to implement, it is crucial to ensure the security of the generated OTPs. This can be achieved by using a strong cryptographic hash function and storing the secret key securely. It is also recommended to enforce additional security measures, such as rate limiting and account lockouts, to protect against brute-force attacks.
Once you have decided on the type of OTP generator and implemented the necessary algorithms, you can integrate it into your application. This typically involves adding a step in the login process where the user is prompted to enter the OTP generated by the program. The entered OTP is then compared to the expected OTP generated by the program. If they match, the user is granted access; otherwise, access is denied.
In conclusion, creating an OTP generator program requires a thorough understanding of the underlying principles and algorithms. By implementing a secure and reliable OTP generator, you can enhance the security of your application and protect user accounts from unauthorized access.
Understanding OTP Generation
Before diving into the implementation details, let’s understand the basic concept behind OTP generation. OTPs are time-based or event-based passwords that are valid for a short period of time or a single use. They are typically generated using a combination of a secret key and a counter or timestamp.
The OTP generation algorithm involves several steps:
- Generate a secret key: A secret key is a random string of characters that is known only to the user and the server. This key is used to generate the OTP.
- Generate a counter or timestamp: The counter or timestamp is used to ensure that each OTP is unique. It can be based on the current time or incremented with each new OTP generation.
- Combine the secret key and counter/timestamp: The secret key and counter/timestamp are combined using a cryptographic function, such as HMAC-SHA1, to generate a unique OTP.
- Truncate the OTP: The generated OTP is usually a long string of characters. To make it more user-friendly, it is truncated to a fixed length (e.g., 6 digits).
Once the OTP is generated, it can be sent to the user via a secure channel, such as SMS or email. The user can then enter the OTP into the authentication system to verify their identity. Since OTPs are time-based or event-based, they provide an additional layer of security compared to traditional static passwords.
It’s important to note that the secret key used for OTP generation should be kept secure and not shared with anyone. If an attacker gains access to the secret key, they can generate valid OTPs and potentially bypass the authentication system.
In addition to the basic OTP generation algorithm described above, there are also variations that can be used to enhance security. For example, some systems use a rolling window of OTPs, where multiple OTPs are generated in advance and stored on both the server and the user’s device. This allows for offline OTP verification and reduces the reliance on a real-time clock.
Overall, OTP generation is a crucial component of modern authentication systems, providing an extra layer of security to protect against unauthorized access. By understanding the underlying concepts and implementing best practices, organizations can ensure the integrity and confidentiality of their systems and data.
Algorithm Structure
Now that we have a basic understanding of OTP generation, let’s outline the algorithm structure for creating an OTP generator program:
- Define the secret key: Start by defining a secret key that will be used to generate the OTP. This key should be kept secure and not shared with anyone. The secret key can be a randomly generated string of characters, such as a combination of letters, numbers, and special symbols. It is important to choose a strong secret key to ensure the security of the OTP.
- Generate a counter or timestamp: Depending on the type of OTP generation (time-based or event-based), generate a counter or timestamp value. For time-based OTPs, you can use the current time in seconds since the epoch. This can be obtained using a programming language’s built-in functions or libraries. For event-based OTPs, you can use a counter that increments with each OTP generation. This counter can be stored in a database or memory for future use.
- Combine the secret key and counter/timestamp: Use a cryptographic function, such as HMAC-SHA1, to combine the secret key and the counter/timestamp value. This will generate a unique OTP. The cryptographic function takes the secret key and the counter/timestamp as input and produces a hash value. The hash value is a fixed-length string that is unique for each combination of secret key and counter/timestamp.
- Truncate the OTP: To make the OTP more user-friendly, truncate it to a fixed length (e.g., 6 digits) by taking a substring of the generated OTP. This can be done by selecting the first 6 characters of the OTP or by using a specific truncation algorithm. Truncating the OTP reduces its length and makes it easier for users to enter or remember.
- Display or use the OTP: Finally, display the generated OTP to the user or use it for further authentication or verification purposes. The OTP can be displayed on a web page, mobile app, or any other user interface. It can also be used for two-factor authentication, where the user is required to enter both their password and the OTP to access a secure system or perform a sensitive operation.
By following this algorithm structure, you can create a robust and secure OTP generator program that can be used in various applications, such as online banking, email verification, or secure login systems. The secret key and the cryptographic functions ensure the uniqueness and randomness of the OTP, while the truncation and display steps make it user-friendly and easy to use. Overall, OTP generation is a crucial aspect of modern security systems, providing an additional layer of protection against unauthorized access and identity theft.
To further enhance the security of the OTP generator program, we can implement additional features such as user input validation and error handling. This will ensure that the program can handle various scenarios and provide a smooth user experience.
One way to implement user input validation is by checking the length and format of the secret key. The secret key should be a string of alphanumeric characters and have a minimum length of, let’s say, 8 characters. We can use regular expressions to validate the secret key before generating the OTP.
Additionally, we can implement error handling to handle any unexpected errors that may occur during the execution of the program. For example, if there is an issue with the HMAC-SHA1 hash generation or if the OTP cannot be generated, we can display an error message to the user and prompt them to try again.
Furthermore, we can add a feature to allow the user to specify the length of the OTP they want to generate. By default, we are currently generating a 6-digit OTP, but some applications may require longer or shorter OTPs. We can modify the `generate_otp` function to accept an optional parameter for the OTP length and update the truncation step accordingly.
Another improvement we can make is to implement a mechanism to store and manage the counter value. Currently, we are using the current timestamp as the counter, but in a real-world scenario, we would need a more robust and secure way to manage the counter value. We can consider using a database or a file system to store and retrieve the counter value, ensuring that it is incremented correctly for each OTP generation.
In conclusion, by implementing user input validation, error handling, customizable OTP length, and a counter management mechanism, we can enhance the security and functionality of the OTP generator program. These additional features will provide a more reliable and user-friendly experience for generating OTPs.

AWS, Technology |
When it comes to managing your domain’s DNS (Domain Name System) infrastructure, reliability and scalability are of utmost importance. That’s where AWS Route 53 comes in. As one of Amazon Web Services’ most popular offerings, Route 53 provides a highly available and scalable DNS service that ensures your domain is always accessible to your users.
What is AWS Route 53?
AWS Route 53 is a cloud-based DNS web service offered by Amazon Web Services. The name “Route 53” is derived from the fact that DNS servers respond to queries on port 53, and it also pays homage to the iconic Route 66 in the United States. Route 53 effectively routes internet traffic to the appropriate resources, such as web servers or load balancers, based on the domain names specified in DNS requests.
Why Choose AWS Route 53?
There are several reasons why AWS Route 53 is a popular choice for managing DNS infrastructure:
1. Reliability and High Availability
Route 53 is designed to provide a highly reliable and available DNS service. It operates on a global network of DNS servers strategically distributed across multiple AWS regions. This ensures that your domain’s DNS records are replicated and served from multiple locations, reducing the risk of downtime and improving overall performance.
2. Scalability
As your online presence grows, you need a DNS service that can handle increased traffic and adapt to changing demands. Route 53 is built to scale, allowing you to handle millions of queries per second with low latency. It automatically scales its infrastructure to accommodate traffic spikes and provides advanced features like Traffic Flow to intelligently distribute traffic across multiple resources.
3. DNS Management Features
Route 53 offers a wide range of DNS management features that give you fine-grained control over your domain’s DNS configuration:
- Domain Registration: You can register new domain names directly through Route 53 or transfer existing domains from other registrars.
- Zone Apex Support: Route 53 allows you to configure DNS records for your domain’s zone apex (e.g., example.com) without the need for additional infrastructure.
- Alias Records: Alias records enable you to map your domain directly to AWS resources like Elastic Load Balancers, CloudFront distributions, or S3 buckets, without the need for CNAME records.
- Health Checks: Route 53 can monitor the health of your resources and automatically route traffic away from unhealthy endpoints.
- Routing Policies: You can use different routing policies, such as simple, weighted, latency-based, geolocation, or failover, to control how Route 53 responds to DNS queries.
4. Integration with AWS Services
As part of the AWS ecosystem, Route 53 seamlessly integrates with other AWS services, allowing you to leverage its capabilities in conjunction with other powerful tools. For example, you can use Route 53 with AWS Elastic Beanstalk to easily deploy and manage your web applications, or integrate it with AWS CloudFormation for automated infrastructure provisioning.
5. Cost-Effective Pricing
Route 53 offers competitive and transparent pricing, with pay-as-you-go rates based on the number of hosted zones, DNS queries, and health checks. The pricing model is designed to be cost-effective, especially for small to medium-sized businesses.
Conclusion
AWS Route 53 is a reliable and scalable DNS service that provides the foundation for your domain’s online presence. With its global network of servers, advanced DNS management features, seamless integration with other AWS services, and cost-effective pricing, Route 53 is a trusted choice for businesses of all sizes. Whether you are hosting a simple website or managing a complex application infrastructure, Route 53 ensures that your domain is always accessible and performs optimally.

Networking, Technology |
In the world of networking and digital communication, the OSI model plays a crucial role in ensuring seamless data transmission. Understanding this model can help demystify the complexities of digital delivery and empower individuals to troubleshoot network issues more effectively.
The OSI Model: An Overview
The OSI (Open Systems Interconnection) model is a conceptual framework that defines the functions of a network into seven distinct layers. Each layer has its own specific responsibilities and interacts with the layers above and below it to facilitate the transmission of data across a network.
Let’s take a journey through the OSI model and explore the purpose and functions of each layer:
Layer 1: Physical Layer
The physical layer is responsible for the actual transmission of data bits over a physical medium, such as cables or wireless signals. It defines the electrical, mechanical, and procedural aspects of the physical connection.
Layer 2: Data Link Layer
The data link layer ensures reliable data transfer between two directly connected devices. It breaks the data into frames and performs error detection and correction. This layer also handles flow control to prevent overwhelming the receiving device.
Layer 3: Network Layer
The network layer is responsible for addressing and routing data packets across multiple networks. It determines the most efficient path for data to travel from the source to the destination device, taking into account factors such as network congestion and availability.
Layer 4: Transport Layer
The transport layer provides end-to-end communication between the source and destination devices. It ensures the reliable delivery of data by segmenting large chunks of data into smaller packets and reassembling them at the receiving end. This layer also handles error recovery and flow control.
Layer 5: Session Layer
The session layer establishes, manages, and terminates communication sessions between two devices. It allows for synchronization and coordination between the sender and receiver, ensuring that data is exchanged in an orderly manner.
Layer 6: Presentation Layer
The presentation layer is responsible for data formatting, encryption, and compression. It ensures that the data sent by the application layer is properly interpreted by the receiving device and vice versa.
Layer 7: Application Layer
The application layer is the layer closest to the end user. It provides services and interfaces for applications to access the network. Examples of application layer protocols include HTTP, FTP, and SMTP.
Why Understanding the OSI Model Matters
Having a solid understanding of the OSI model is essential for troubleshooting network issues. By knowing the functions of each layer, network administrators can pinpoint the layer at which a problem is occurring and take appropriate action.
For example, if a user is unable to access a website, the issue could be at the application layer, such as a misconfigured web server. On the other hand, if the problem lies in establishing a connection, it may be related to the physical or data link layer.
By following a systematic approach and ruling out each layer one by one, network administrators can efficiently identify and resolve network problems, leading to improved network performance and user experience.
In Conclusion
The OSI model provides a structured framework for understanding the complexities of digital delivery. By breaking down the network functions into seven distinct layers, it enables network administrators to troubleshoot and resolve issues more effectively.
Whether you’re a seasoned network professional or someone interested in learning more about networking, gaining a solid understanding of the OSI model is a valuable skill that will enhance your ability to navigate the digital world with confidence.

Ideas, Learning, Scripting, Technology, Web Design, Web Development |
Introduction
When it comes to building successful products and websites, user experience (UX) design plays a crucial role. UX design is more than just making things look visually appealing; it focuses on creating a seamless and intuitive experience for users. In this article, we will delve into the importance of UX design as a fundamental step in every project, and how it can significantly impact the success and usability of a product.
The Role of UX Design
UX design involves understanding the needs and expectations of users and designing a product that meets those requirements effectively. It encompasses various aspects such as user research, information architecture, interaction design, and visual design. The primary goal of UX design is to enhance user satisfaction by providing a positive and intuitive experience.
By incorporating UX design into a project, businesses can achieve several key benefits:
1. Improved User Satisfaction
UX design focuses on creating user-centric solutions by understanding user behavior, preferences, and pain points. By conducting thorough user research and usability testing, designers can identify and address potential issues early on in the development process. This leads to a more satisfying user experience and increases the likelihood of user engagement and retention.
2. Increased Conversion Rates
A well-designed user experience can significantly impact conversion rates. By optimizing the user journey and reducing friction points, UX design can guide users towards their desired actions, such as making a purchase or signing up for a service. A seamless and intuitive user experience can boost conversions and ultimately drive business growth.
3. Enhanced Brand Perception
UX design is closely tied to brand perception. A poorly designed and frustrating user experience can leave a negative impression on users, damaging the reputation of a brand. On the other hand, a well-designed and user-friendly experience can enhance brand perception, instilling trust and credibility in users.
4. Cost and Time Savings
Integrating UX design early in the project lifecycle can save both time and resources. By identifying and addressing usability issues early on, businesses can avoid costly redesigns and rework later in the development process. This proactive approach helps streamline the overall project timeline and ensures a more efficient and effective product development process.
The UX Design Process
The UX design process typically involves the following key steps:
1. User Research
Understanding the target audience is crucial for designing a successful user experience. User research involves gathering insights about user behaviors, needs, and motivations through methods such as surveys, interviews, and user testing. This data forms the foundation for creating user personas and identifying user pain points.
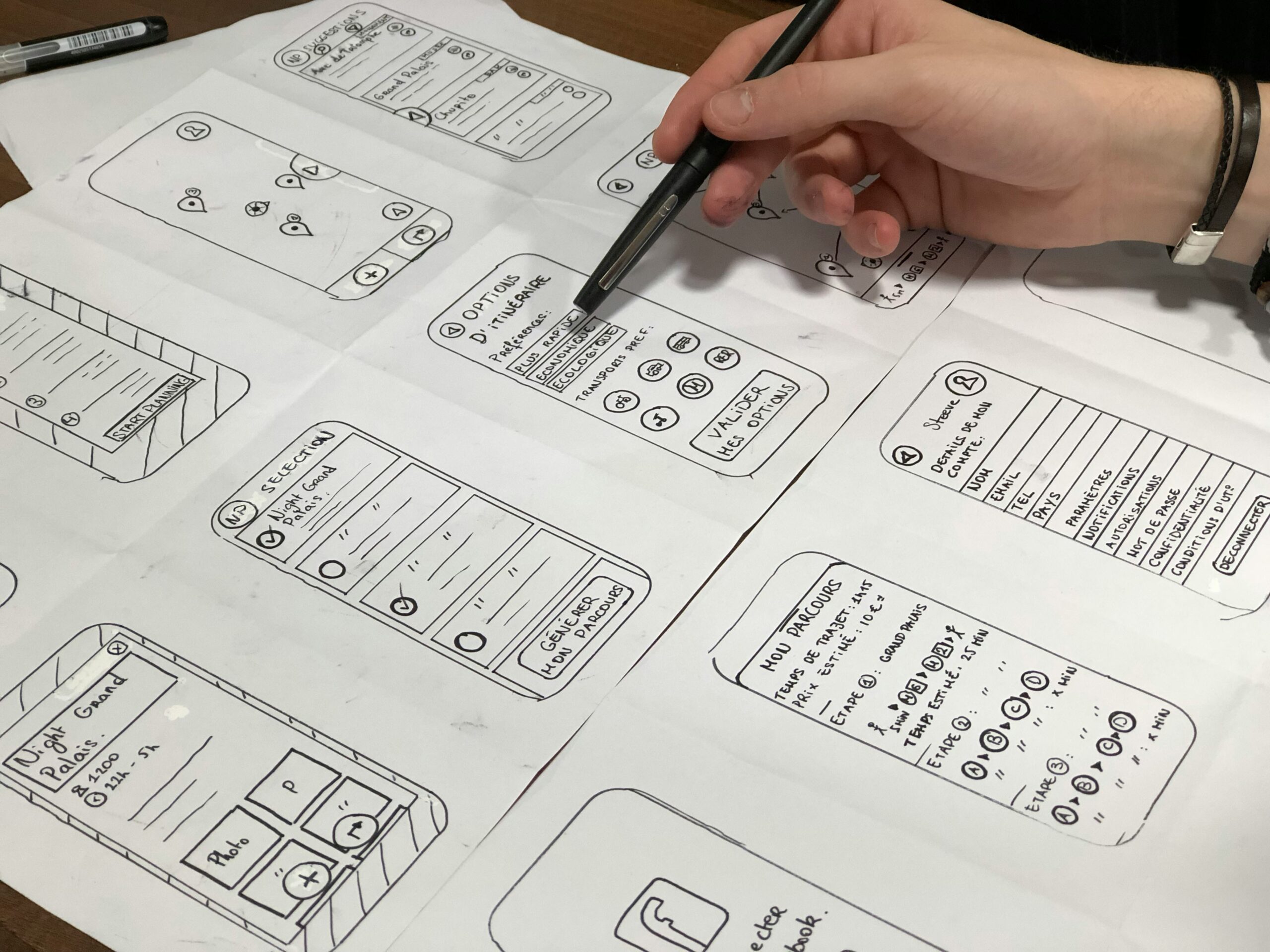
2. Information Architecture
Information architecture focuses on organizing and structuring content in a way that is logical and intuitive for users. This step involves creating sitemaps, wireframes, and user flows to define the overall structure and navigation of the product.
3. Interaction Design
Interaction design is concerned with defining how users interact with the product. It involves designing user interfaces, creating interactive prototypes, and ensuring that the product’s functionality aligns with user expectations.
4. Visual Design
Visual design focuses on creating visually appealing and aesthetically pleasing interfaces. It involves selecting colors, typography, and visual elements that align with the brand identity and enhance the overall user experience.
5. Usability Testing
Usability testing is a crucial step in the UX design process. It involves observing users as they interact with the product and gathering feedback on its usability. This feedback helps identify areas for improvement and ensures that the final product meets user expectations.
Conclusion
UX design is an essential step in every project, regardless of the industry or product. By prioritizing user satisfaction, businesses can create products that not only meet user needs but also drive business growth. Incorporating UX design into the project lifecycle can lead to improved user satisfaction, increased conversion rates, enhanced brand perception, and cost and time savings. By following a structured UX design process, businesses can create products that not only look great but also provide a seamless and intuitive user experience.
Remember, UX design is not a one-time step, but an ongoing process. Regularly gathering user feedback and making iterative improvements based on user needs and expectations is key to creating exceptional user experiences.

Technology |
Introduction
Python AI, or Artificial Intelligence, has become increasingly popular due to its versatility and ease of use. With Python AI, you can create applications that can perform complex tasks, such as natural language processing, image recognition, and predictive analytics. In this article, we will guide you through the process of building a simple application using Python AI.
Step 1: Setting Up the Environment
The first step in building a Python AI application is to set up your development environment. You will need to install Python and a few additional libraries that are commonly used in AI development. The most popular libraries for AI in Python are TensorFlow, Keras, and scikit-learn. You can install these libraries using the pip package manager.
Once you have installed Python and the necessary libraries, you are ready to start building your application.
Step 2: Defining the Problem
Before you begin coding, it is important to clearly define the problem you want your application to solve. This will help you determine the type of AI algorithm you need to implement. For example, if you want to build a chatbot, you may use natural language processing algorithms. If you want to build a recommendation system, you may use collaborative filtering algorithms.
Defining the problem will also help you gather the necessary data and determine the evaluation metrics for your application.
Step 3: Gathering and Preparing Data
AI applications rely heavily on data. You will need to gather and prepare the data that your application will use for training and testing. The data should be representative of the problem you are trying to solve.
Once you have gathered the data, you will need to preprocess it. This may involve cleaning the data, removing outliers, and transforming the data into a format that can be used by your AI algorithm. You may also need to split the data into training and testing sets.
Step 4: Choosing and Implementing an AI Algorithm
Now that you have your data ready, you can choose an AI algorithm that is suitable for your problem. There are various types of AI algorithms, including supervised learning, unsupervised learning, and reinforcement learning.
If you are new to AI, it is recommended to start with a simple algorithm, such as linear regression or k-nearest neighbors. These algorithms are easy to implement and understand. As you gain more experience, you can explore more complex algorithms.
Step 5: Training and Evaluating the Model
Once you have implemented your AI algorithm, you can train it using the training data. During the training process, the algorithm will learn from the data and adjust its parameters to minimize the error.
After training the model, you should evaluate its performance using the testing data. There are various evaluation metrics you can use, depending on the problem you are solving. Common evaluation metrics include accuracy, precision, recall, and F1 score.
Step 6: Deploying the Application
Once you are satisfied with the performance of your AI model, you can deploy your application. This may involve creating a user interface, integrating the AI model into the application, and deploying it to a server or the cloud.
It is important to monitor the performance of your application after deployment and make any necessary improvements or updates.
Conclusion
Building a simple application on Python AI is an exciting and rewarding process. By following the steps outlined in this guide, you can create an application that can perform intelligent tasks. Remember to start with a clear problem definition, gather and prepare the necessary data, choose and implement an AI algorithm, train and evaluate the model, and finally, deploy the application. With practice and experience, you can continue to enhance and expand your Python AI applications.